Merill’s Blog
Graph X-Ray 1.1.10: Firefox support, better PowerShell generation, and a sharper DevTools experience
Graph X-Ray has always had one simple goal: make Microsoft Graph easier to learn, inspect, and automate. Open the Microsoft admin portal, perform the action you care about, and Graph X-Ray shows you the Graph calls happening behind the scenes so you can turn those clicks into code.
With the 1.1.10 release, Graph X-Ray takes a big step forward. The headline feature is Firefox support, which means Graph X-Ray is now available across Microsoft Edge, Google Chrome, and Mozilla Firefox. This release also adds a new PowerShell generation path based on Invoke-MgGraphRequest, improves reliability when the upstream snippet service has issues, adds filtering and request counts to the DevTools panel, expands portal coverage, and formally moves the project under the AGPL-3.0 license.
Install Graph X-Ray from graphxray.merill.net or head straight to the browser stores:
Graph X-Ray now supports Firefox
The biggest update in this release is full Firefox support, contributed in large part by Jorge Suarez (@jorgeasaurus) in PR #4.
This was more than a checkbox change. Firefox and Chromium-based browsers have meaningful differences in extension APIs, manifest support, background scripts, DevTools integration, and packaging requirements. Graph X-Ray now handles those differences cleanly with a Firefox-specific build and compatibility layer.
The result is simple for users: Graph X-Ray now works in Firefox. If Firefox is your daily browser, you no longer need to switch to Edge or Chrome just to inspect Microsoft Graph calls.
PowerShell generation now has an Invoke-MgGraphRequest path
The second major improvement is PowerShell reliability.
Graph X-Ray has traditionally used Microsoft’s DevX snippet API to generate language-specific snippets. That works well for many languages, but the PowerShell endpoint began returning failures, which meant PowerShell snippets could disappear even though Graph X-Ray had captured the request correctly. This was tracked in issue #8 and fixed through PR #11, again thanks to @jorgeasaurus.
Graph X-Ray now includes a local PowerShell snippet generator that uses Invoke-MgGraphRequest from the Microsoft Graph PowerShell SDK. That gives users a reliable fallback when the external snippet API is unavailable and also adds a dedicated PowerShell option for people who prefer the direct request style.
For example, a captured request can now become:
Invoke-MgGraphRequest -Method GET -Uri "https://graph.microsoft.com/v1.0/me"
For requests with JSON bodies, Graph X-Ray builds a PowerShell hashtable and sends it as JSON:
$params = @{
"displayName" = "Test User"
"accountEnabled" = $true
}
Invoke-MgGraphRequest -Method POST -Uri "https://graph.microsoft.com/v1.0/users" -Body ($params | ConvertTo-Json -Depth 10) -ContentType "application/json"
The generator handles nested objects, arrays, booleans, numbers, $null, string escaping, request bodies, and ConsistencyLevel: eventual for advanced query scenarios. PowerShell snippets also render immediately while Graph X-Ray attempts to upgrade to a server-generated snippet in the background when appropriate.
The new path makes Graph X-Ray less dependent on an external service and gives admins a snippet that is easy to understand, edit, and run.
New REST mode for people who want the raw request
This release also adds a REST language option in the DevTools panel.
Sometimes you do not want a generated SDK sample. You just want the clean request URL so you can paste it into Graph Explorer, an HTTP file, a script, or your own tooling. REST mode returns the raw URL directly and gives batch sub-requests their own copyable REST entries.
That makes Graph X-Ray more useful as an inspection tool, not just a script generator.
Filtering, counts, and a cleaner request view
As Graph X-Ray captures more traffic, especially in Microsoft admin portals that make several calls for a single UI action, the DevTools panel can fill up quickly. Version 1.1.10 adds a much better way to navigate that stream.
The request view now includes:
- A filter box for narrowing by URL.
- Method filters such as
GET,POST,PATCH, andDELETE. - Resource filters that group related Graph resources.
- Domain filters when Ultra X-Ray mode is enabled and multiple domains are present.
- Request counts showing the total captured requests and the filtered subset.
- Better handling for batch requests, including per-request filtering inside a batch.
- A collapsible batch execution snippet so individual request snippets stay easier to scan.
- Color-coded URL rendering for hosts, paths, query keys, and query values.
These changes make Graph X-Ray easier to use during real admin workflows. You can perform an action in Entra, Intune, Power Platform admin center, or another supported portal, then quickly narrow the captured requests to the exact call you need.
Better batch request handling
Microsoft admin portals often use Graph batch requests. Those are efficient for the portal, but they can be harder for humans to inspect because several logical requests are wrapped in a single network call.
Graph X-Ray now does more work to make batch requests useful:
- Individual batch requests get their own generated snippets.
- Batch item URLs are normalized more reliably.
- Filtering works against the sub-requests inside a batch.
- REST mode can show each individual batch URL.
- The batch execution snippet is still available, but collapsed by default so it does not dominate the view.
That means a single captured batch can now be unpacked into the specific Microsoft Graph operations that matter for your automation.
Expanded portal and cloud coverage
Graph X-Ray continues to support Microsoft Graph endpoints across Microsoft cloud environments:
graph.microsoft.comgraph.microsoft.usdod-graph.microsoft.usmicrosoftgraph.chinacloudapi.cn
This release also expands Ultra X-Ray coverage with additional admin portal domains, including:
admin.powerplatform.microsoft.comadmin.cloud.microsoft
These additions close community-reported gaps from issue #7 and issue #9, where users reported missing capture support for Microsoft 365 admin center Edge settings and Power Platform admin center activity.
Ultra X-Ray remains the place for non-Graph or internal admin API visibility, while the standard Graph X-Ray experience focuses on Microsoft Graph calls.
Graph X-Ray is now AGPL-3.0 licensed
This release also formalizes the project license as GNU Affero General Public License v3.0, with package metadata set to AGPL-3.0-only. The licensing update was handled in PR #12.
Graph X-Ray remains free and open source, and the license now makes that explicit in the repository and package metadata.
Thank you to the contributors
This release had several important contributions and community reports.
Special thanks to:
- Jorge Suarez (@jorgeasaurus), who contributed the Firefox support work and the PowerShell reliability improvements.
And thank you to the community members who reported issues that shaped this release:
- @WigF1, who reported that PowerShell snippets were not appearing.
- @tlourey, who reported missing capture support for Edge settings in the Microsoft 365 admin center.
- @askaresh, who requested Power Platform admin center support.
Try the new release
If you work with Microsoft 365, Entra, Intune, Power Platform, or Microsoft Graph automation, install the latest version of Graph X-Ray and try it in your browser of choice.
Open an admin portal, open DevTools, switch to the Graph X-Ray panel, perform the action you want to automate, and copy the generated request or script.
Graph X-Ray is here to help you answer the question every Microsoft 365 admin eventually asks:
What did that button actually do?
Install Graph X-Ray at graphxray.merill.net or view the source on GitHub.
Share on
TwitterUninstall-Graph PowerShell
The Graph PowerShell module is a complicated beast. It has multiple modules and due to various reasons you might want to get back to a clean slate of no Graph PowerShell modules in your system.
To solve this I built a module that does just one thing
Uninstall-Graph
You can get it at uninstall-graph.merill.net.
It basically runs through multiple times to uninstall all the modules and then finally cleans out the folders for the ones that are stubborn.
Remember to restart a fresh PowerShell session after running this.
Why is the Graph PowerShell module so special?
For starters, some graph modules depend on other graph modules then you have various non-Microsoft modules (like Maester) that rely on Graph modules.
This means uninstalling them is not as simple as running
Uninstall-Module Microsoft.Graph
You would typically see something like this error.
PackageManagement\Uninstall-Package : The module 'Microsoft.Graph.Applications' of version '2.12.0' in module base folder 'C:\Program Files\WindowsPowerShell\Modules\Microsoft.Graph.Applications\2.12.0' cannot be uninstalled, because one or more other modules 'Microsoft.Graph' are dependent on this module. Uninstall the modules that depend on this module before uninstalling module 'Microsoft.Graph.Applications'.
Why would you need to uninstall Microsoft Graph in the first place?
Well the most common reason is that you end up with different versions of the various Graph PowerShell modules and one day you will be hit errors like this
Could not load file or assembly 'Microsoft.Graph.Authentication, Version=2.8.0.0, Culture=neutral,PublicKeyToken=31bf3856ad364e35' or one of its dependencies. The system cannot find the file specified.
or
Import Graph module fails with Could not load file or assembly 'Azure.Core, Version=1.39.0.0, Culture=neutral, PublicKeyToken=92742159e12e44c8' or one of its dependencies. The system cannot find the file specified
or something similar.
So getting back to a clean slate and then installing the modules afresh is my preferred solution for this problem.
I’m keen on having this module address all the edge cases when it comes to uninstalling the Graph PS modules. So if you come across any issues please raise them on GitHub. Thanks!
Share on
TwitterHow I create the Entra.Chat podcast
All of the apps/tools I use below are free ($0) except
- Riverside Standard (I got a 50% discount coupon so paid $90 for first year)
- Podcast Chapters which was a one time $20.
- Fedica - for cross posting podcast clips ($10 per month)
I run a weekly podcast with a new guest for each episode.
This is a solo effort where I do EVERYTHING (schedule, interview, edit, publish).
So I am constantly scheduling, recording, editing and publishing my podcast. Even reaching out and keeping track of the people I reached out is crazy since I might have DMd on LinkedIn, Twitter, Email, Teams/Slack.
I tried various note taking apps and calendar integrations like Notion but couldn’t get a handle on things.
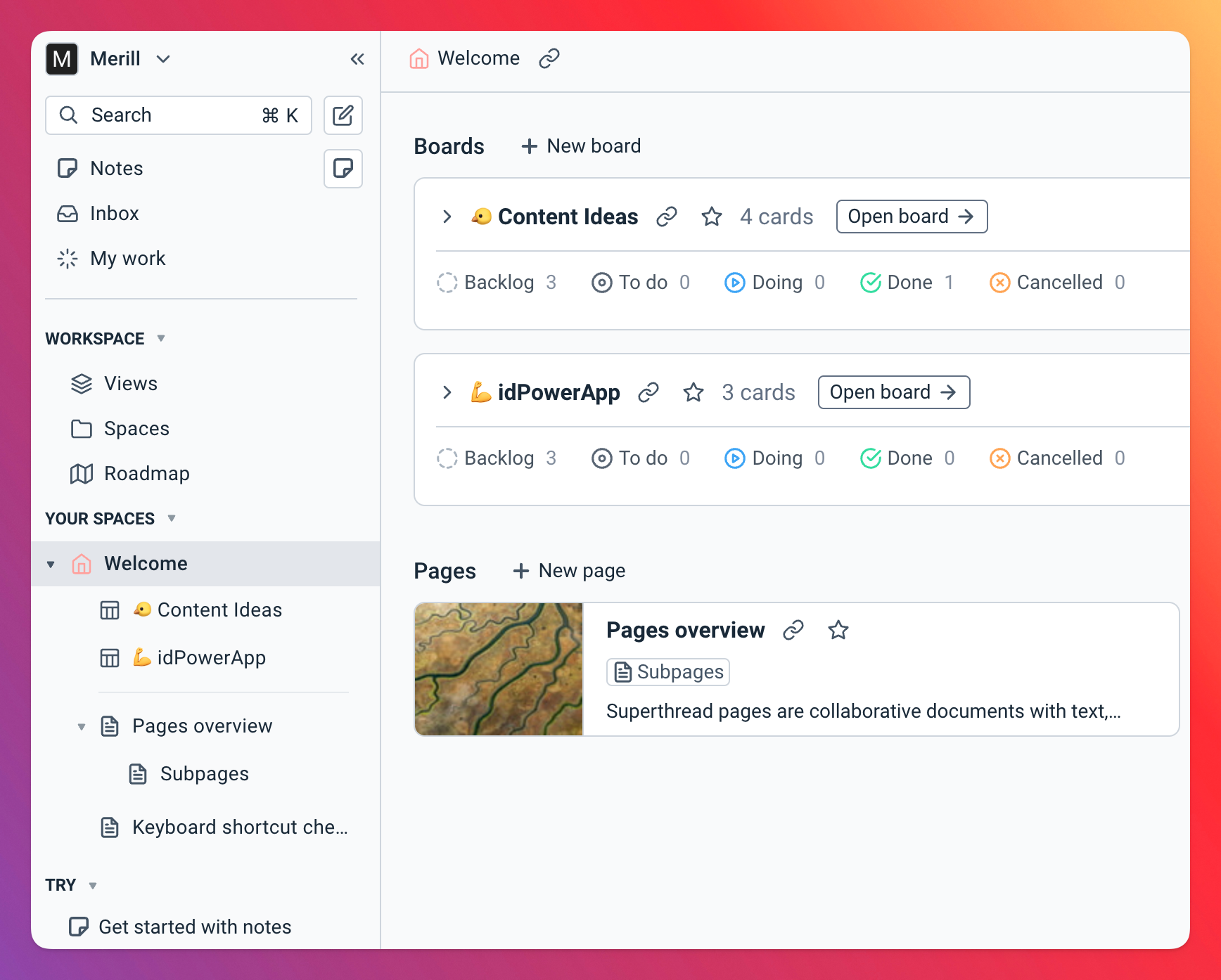
What finally worked for me is
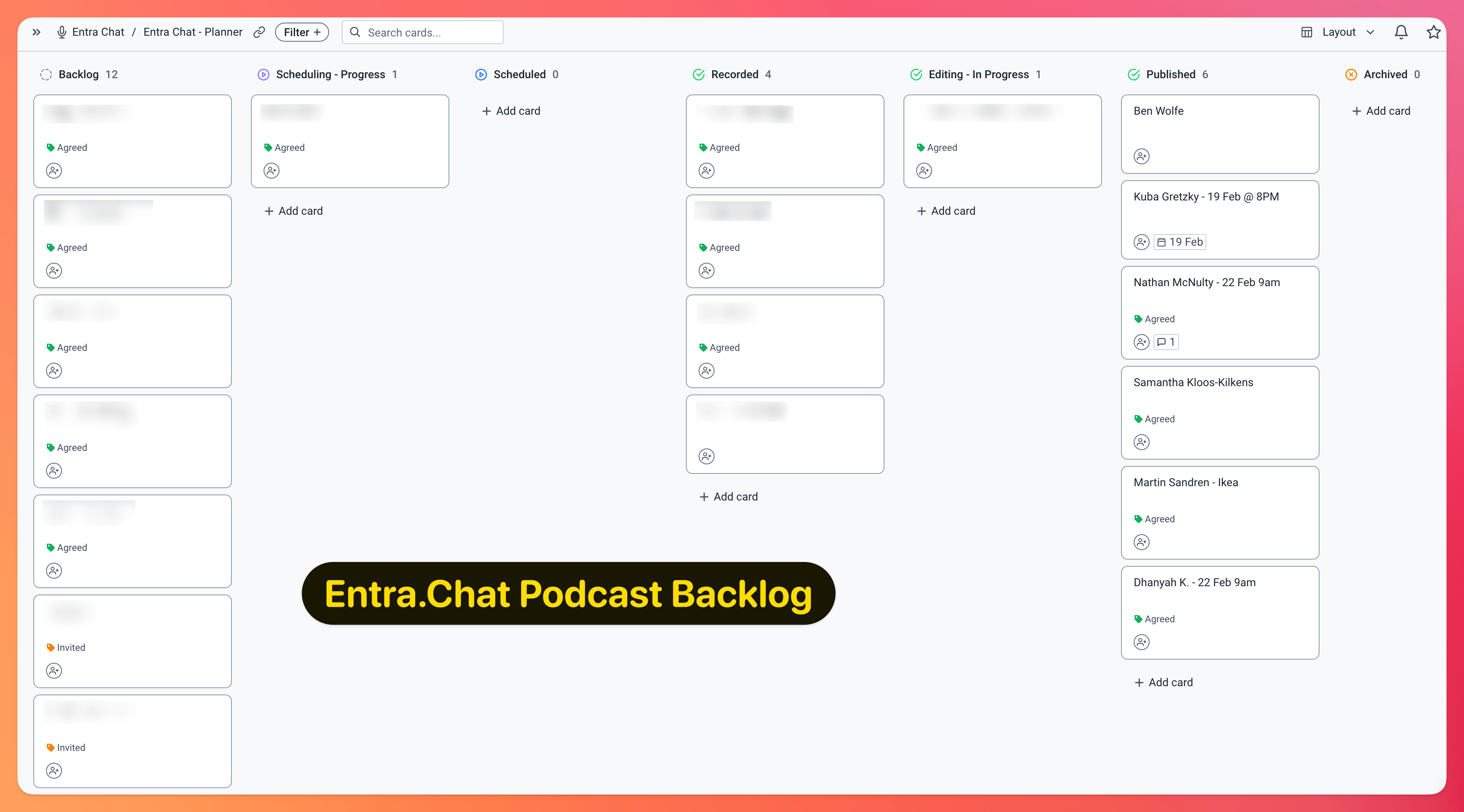
Using it I was able to create a kanban where I progressed each guest through a workflow. They went from
- Backlog - People I want to get on the podcast
- Scheduling - People I’ve reached out to (this card has status us Invited/Agreed) if they say yes I tag as Agreed so I know I can schedule them.
- Scheduled - This is once I have them locked in for a date
- Recorded - These are ones I’ve completed recording but haven’t edited or published
- Editing In Progress - These are ones that I’m editing
- Published - These are ones that have gone out to everyone.
Superthread has a rich notes page that is linked to the card for each person/episode. This way I can quickly drill into the note where I store questions and add in notes during the meeting.
I like it so much I use it for tracking my content ideas and ideas for the apps I’m building.
Podcast Editing Process
Okay, now to the actual editing and publishing process (I use Riverside to edit)
I publish video to YouTube and Spotify and audio to everywhere else. I use Substack as my pod website, audio file host.
Here’s my workflow (I keep this in an .md file and keep refining them each week (One day I’m hoping to build an AI agent that automates all this)
# Podcast creation process
## Edit in Riverside
- In Riverside, edit the podcast by listening to the audio and making cuts as needed.
- Use the smart scene option to generate automatic multicam cuts.
- Change video layout (eg me scratching my head)
- If track is not in sync with video click through and add a delay to the track.
Export a 4k version of the video (only use the remove watermark option on export).
## DaVinci Resolve
- Import the video into DaVinci Resolve.
- Use the Assets in this folder (intro, outro etc)
- Take two or three interesting clips from the content and insert them at the beginning.
- The YT thumbnail should be relevant to the first clip or overall theme of the podcast.
Render YouTube 4k preset and audio only with mp3 audio.
## Titles, Chapters and Description
- Upload audio track to substack to create transcript and download it.
- Use the prompt.md in Gemini to generate titles, chapters and description.
- Create a chapters.csv file with the chapters and timestamps generated by Gemini.
- Use Podcast Chapters (https://chaptersapp.com/) and import the mp3, csv and add images
and chapter titles.
I download the transcript generated by Substack (they do it for free!) and copy/paste the prompt and attach the file to create the notes as well as the csv file for burning the chapter markers and notes into the mp3 file (using chaptersapp.com).
Once I burn the .mp3 with chapter notes I re-upload it to Substack (this is the version that gets sent out).
Podcast clips
I create about 5-6 short clips out of the recording. Because I don’t have the premium version in Riverside I create a portrait video version in Riverside, export it and then use Da Vinci to cut out about 5-6 short clips that are 1-2 min long.
I then use Fedica (a paid service) to schedule and publish one clip every day of the week (plus I sprinkle some for future dates). These get cross posted to all the social media including YT Shorts and TikTok.
So what do you think? What areas would you improve on this? Anything that I should drop? Things I should do to improve the process?
Share on
TwitterService Principal as a 'Plan B' emergency access break-glass account
In the world of Microsoft Entra ID management, few topics generate as much passionate debate as emergency access strategies.
Recently, I posed this question in a poll on LinkedIn and X:
What do you think of using Apps (Service Principals) as a ‘Plan B’ emergency access account?
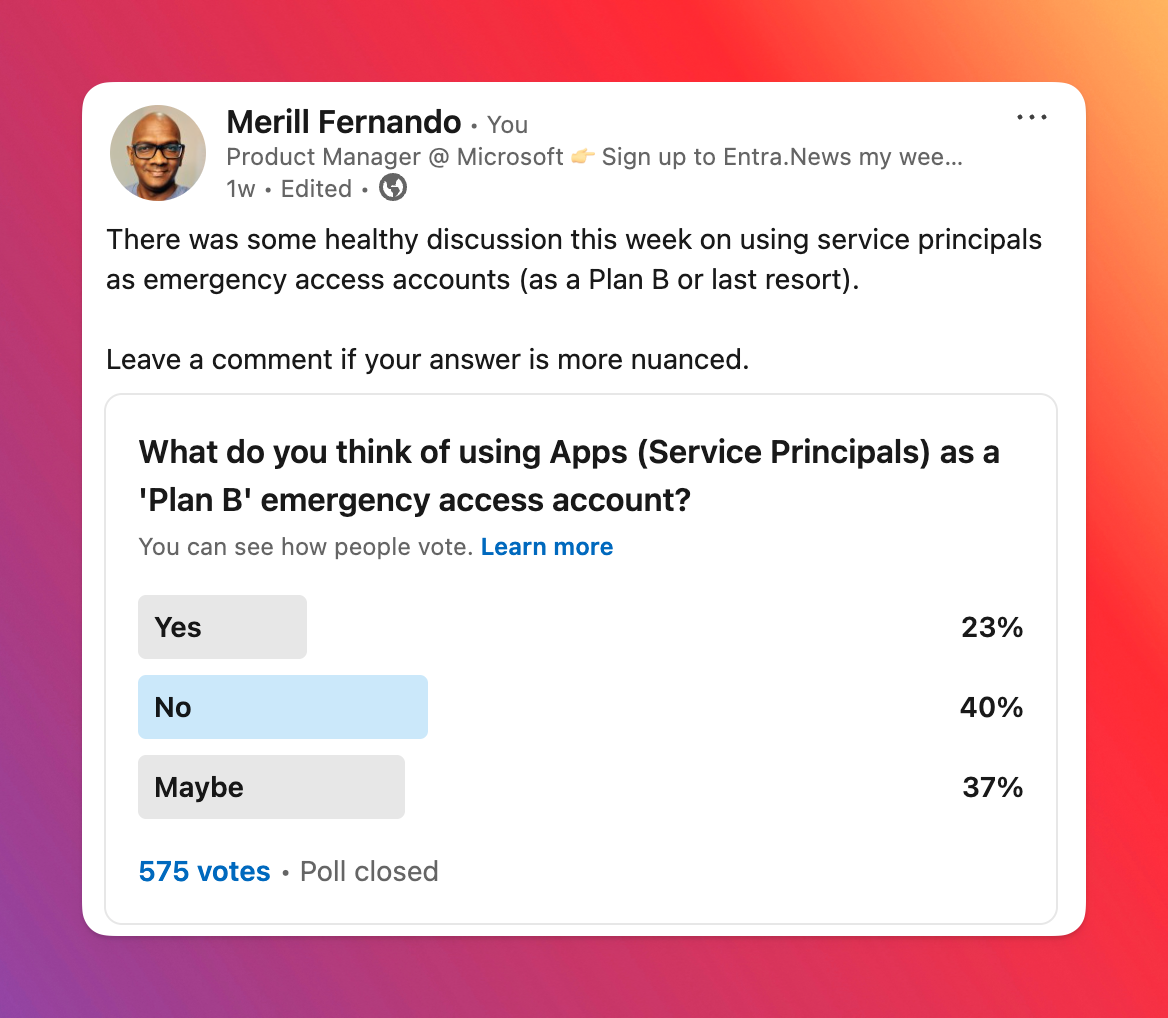
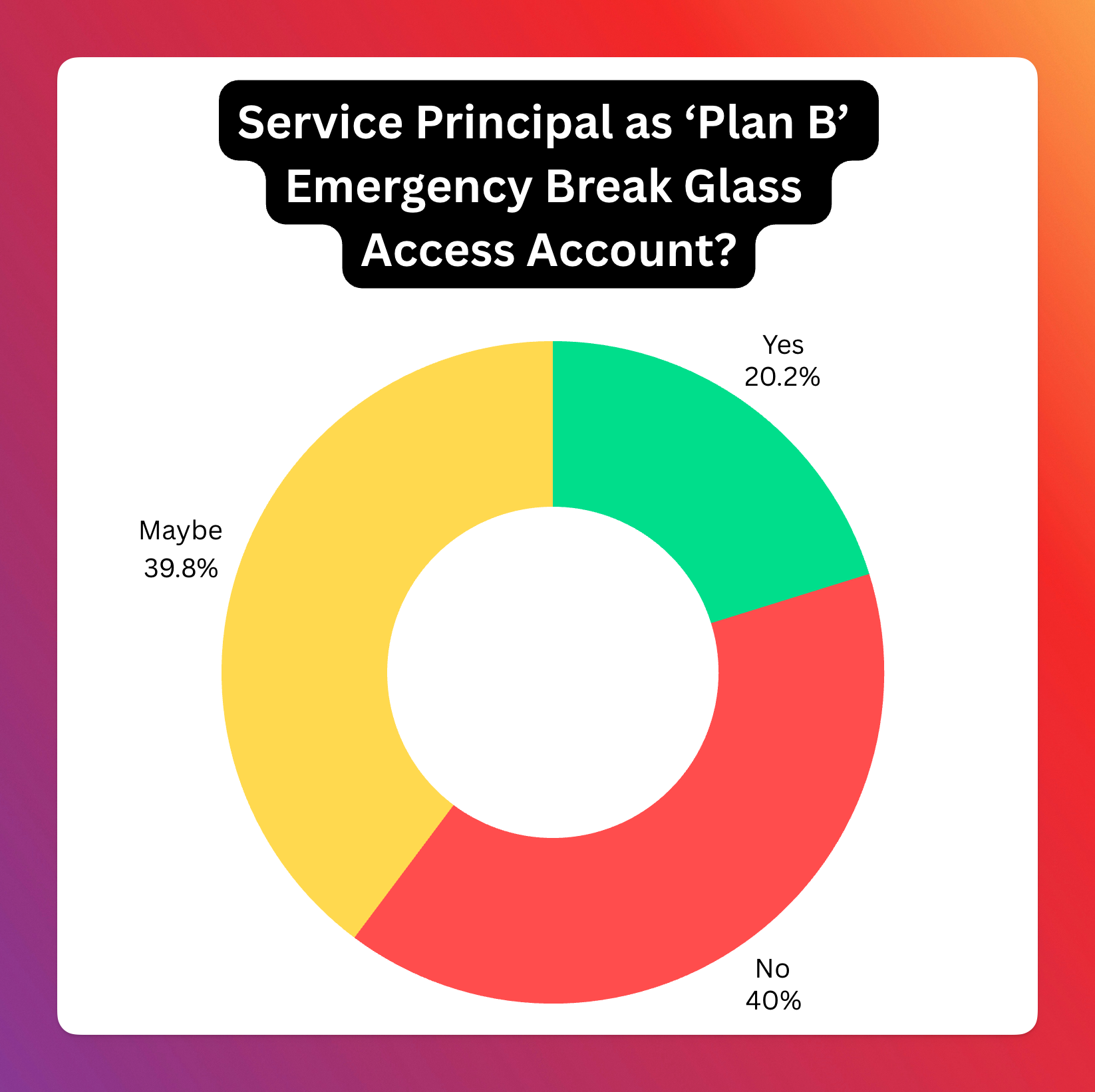
Here’s the combined results from the 817 votes.
This split reflects the nuanced nature of the topic, with no clear consensus. In this blog post, I’ll break down the approach of assigning a Global Administrator (GA) role to an SP for emergency access, analyze the pros and cons based on community feedback, and share my personal take on the matter.
Why emergency access accounts?
Getting locked out of your Entra tenant is the stuff of nightmares for any IT administrator or security professional. Whether it’s a misconfigured Conditional Access policy, a lost or broken multi-factor authentication device, or an expired credential, the inability to access your critical cloud environment can bring operations to a grinding halt.
Microsoft’s recommendation has been to set up a “break-glass” or “emergency access” user account. These highly privileged accounts are kept under strict control, excluded from standard Conditional Access policies and secured with robust methods like FIDO2 keys stored securely offsite. Their usage is heavily monitored and alerts are triggered immediately upon sign-in.
But in the evolving landscape of cloud identity, a new idea has surfaced, sparking considerable debate: What about using an Application (specifically, a Service Principal) with Global Administrator permissions as an emergency access mechanism?
This approach hinges on the fact that Service Principals authenticate differently than users, often using certificates or secrets, which bypasses user-focused Conditional Access policies. The idea is to create a Service Principal, grant it the Global Administrator Entra role, and secure its credentials (ideally a certificate on a hardware security module like a YubiKey) and monitor its activity rigorously.
The earliest reference for this approach that I’ve seen is this reddit post from 2023 ‘Using Service principal as Azure AD Break glass access’. At that time I dismissed the idea, but lately I’ve seen quite a few posts on various forums where admins had locked themselves out of their tenant and it got me thinking about using SPs.
So that’s where the poll came in - “What do you think of using Apps (Service Principals) as a ‘Plan B’ emergency access account?” The results, based on 817 votes, were quite telling:
- Yes: 165 (20.2%)
- No: 327 (40.0%)
- Maybe: 325 (39.8%)
The poll results clearly indicate a significant level of hesitation or outright opposition to this approach. The combined “No” and “Maybe” votes represent nearly 80% of the responses, suggesting that while there’s some interest or recognition of potential edge cases (“Maybe”), the majority are either against it or highly skeptical.
Let’s delve into the lively discussion that followed to understand the reasoning behind these votes.
Analysis of Community Responses: The Pros and Cons Unpacked
Arguments Against (The “No” Votes and Skeptical “Maybe”s)
- Lack of MFA: Service Principals cannot natively perform multi-factor authentication in the same way a user account does. While certificate-based authentication is strong, it’s seen by many as not a direct equivalent to user+MFA.
- Credential Management Hell: The security relies entirely on credential security (secrets or certificates). Many expressed concern about managing these.
- Privilege Escalation Path: The
App AdministratorandCloud Application Administratorroles can manage credentials for Service Principals. If not tightly controlled (e.g., via PIM), an attacker could gain GA access. - Complexity and “Hackiness”: Adds unnecessary complexity that introduces risk.
- Lack of Dedicated Controls: No Restricted Administrative Units (RAUs) for Service Principals.
- Workload Identity CA Dependency: Many organizations haven’t implemented Workload Identity CA policies.
- Doesn’t Solve Core Problems: Doesn’t address root causes of lockouts (poor policy design).
Arguments For or Accepting in Specific Cases
- Bypassing Restrictive CA Policies: A Service Principal can circumvent user-based CA policies that might block all user sign-ins.
- MSPs and Scaling: Managing physical FIDO keys across numerous clients is logistically challenging. An SP approach could be more scalable.
- Requires a Robust Framework: Certificate on HSM, comprehensive monitoring, clear boundaries, protection against modification.
- Microsoft Should Build It: Microsoft should create a built-in, purpose-designed recovery account feature.
- Better Than Poor User Break-Glass: A well-implemented SP break-glass could be more secure than poorly secured user break-glass accounts.
Conclusion from the Responses
The community sentiment: Using a Service Principal with GA rights as a general break-glass is largely viewed with skepticism (combined 80% “No” and “Maybe”).
My Personal Opinion
(Personal opinion, not representing Microsoft)
I lean towards “Yes” for specific types of tenants:
- Increased Lockout Vectors: The ways to lock yourself out have proliferated.
- Difficulty of Recovery: Recovering access via Microsoft Support is difficult and time-consuming by design.
- Tenant Type Matters:
- Entra ID Free Tenants, M365 Dev tenants: (Yes) - No clear way to prove ownership.
- Customers with Enterprise Agreements: Diminished need (Maybe).
- Production tenants where your CEO can call Satya: Do you even need break-glass accounts?
Creating a Break-Glass Service Principal account
- Create Emergency Access Service Principal: Dedicated app. Multi-tenant SPs cannot be blocked by Workload ID CA policies in other tenants (today).
- Grant Entra GA role: Hard to predict what can go wrong; wide role needed.
- Secure Credentials with HSM Certificate: Generate CSR on a local HSM (YubiKey). Private key never leaves the HSM.
- Robust Monitoring: Immediate, high-priority alerting whenever the SP signs in. SIEM integration, KQL queries, multi-channel alerts.
- Redundancy for Monitoring: Separate, independent heartbeat check system.
Someday I hope to build a PowerShell module or an app that makes it super easy to set this up correctly and manage it.
References and further reading
- How to Configure an Emergency Access App in Entra ID - Lokesh
- M365 Breakglass Maturity Model - Graham Gold
- Attacker’s Breakdown: M365 Break Glass Maturity - Elli Shlomo
Share on
TwitterMicrosoft 365 Dev Program Update
There’s not much meat in it but it hints at Microsoft working on making it available again (don’t quote me on this).
You can read the announcement at Exciting updates coming to the Microsoft 365 Developer Program.
I like some of the improvements like being able to add new licenses to the tenant, etc.
Hopefully we’ll see more details coming through and this launching.
Share on
TwitterUsing Pester to regression test Maester tests
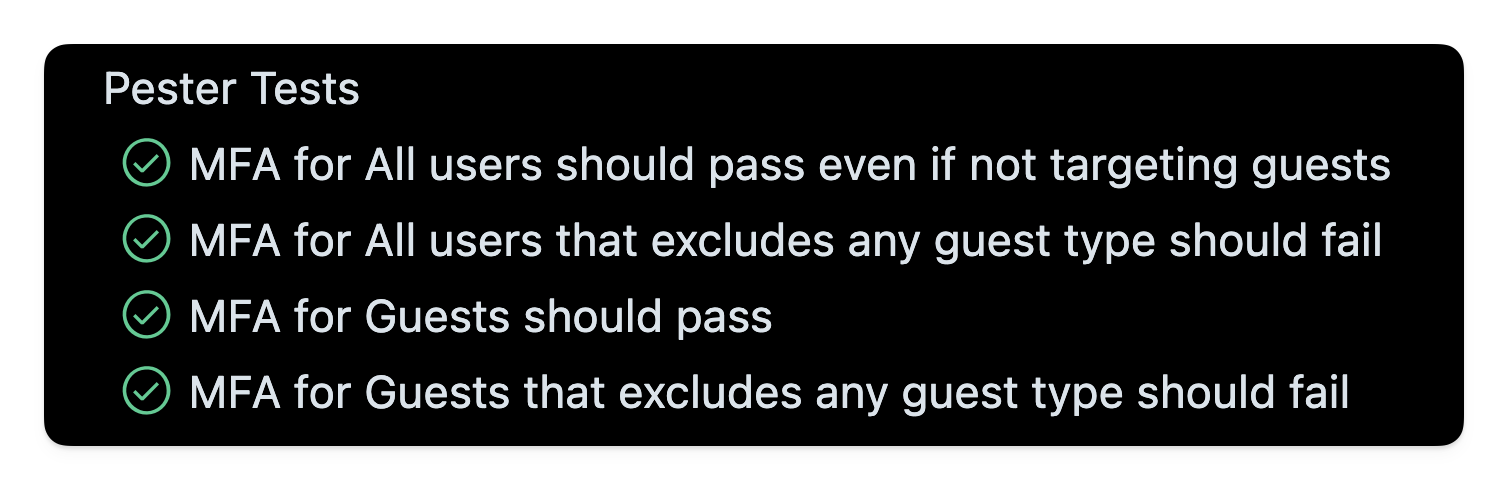
Pester tests for Maester tests!
I was fixing a Maester bug and thought it would be good to share my process for going about it.
We start off with a Maester bug (Issue with MT. 1016 #804). In this instance the tenant had a CA policy for All Users but did not have one explicitly targeting guests.
While it’s always a better practice to have a separate set of policies for guests, Maester should not penalise them for this. Technically they are in the clear since MFA being applied to all users including guests.
Now the existing code for this check was getting too long and adding more parts to this expression was going to make it hard to maintain.
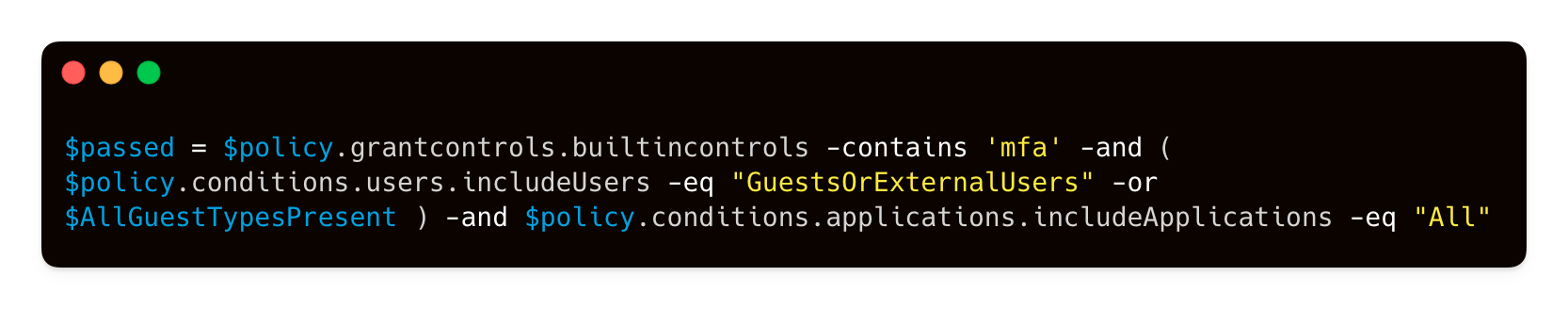
GitHub Copilot to the rescue! I prompted and got a much cleaner implementation and was able to add the additional check.
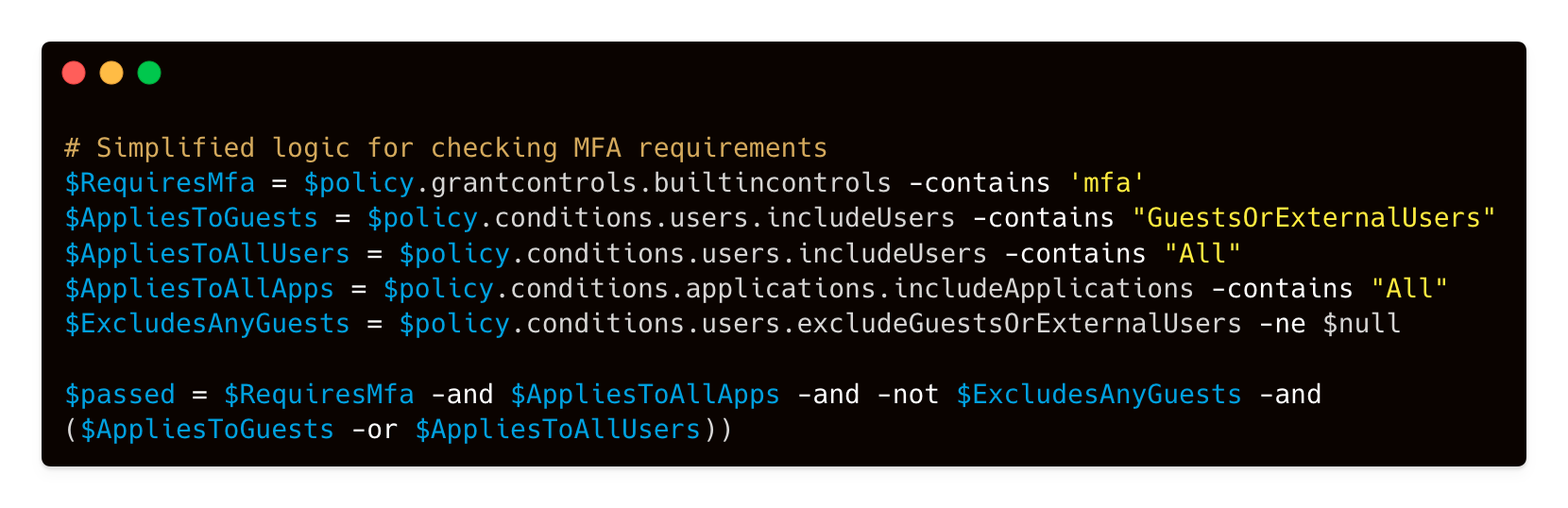
Now we need to test if it’s working as expected. This involves creating a bunch of CA policies to test and how do we make sure it keeps working with future changes?
That’s where Pester tests come in. I created a bunch of Pester tests to simulate various types of CA policies. Some targeting all users, others targeting just guests and also checking if any type of guest had been excluded.

How I went about this was copying out the json of the CA policy. This one here targets guests but excludes the B2B Collab Guest type. This type of policy should be failed by Maester since the tenant is missing an important chunk of guest users being required to have MFA.

- Maester Test: Test-MtCaMfaForGuest.ps1
- Pester Test File: Test-MtCaMfaForGuest.Tests.ps1
Share on
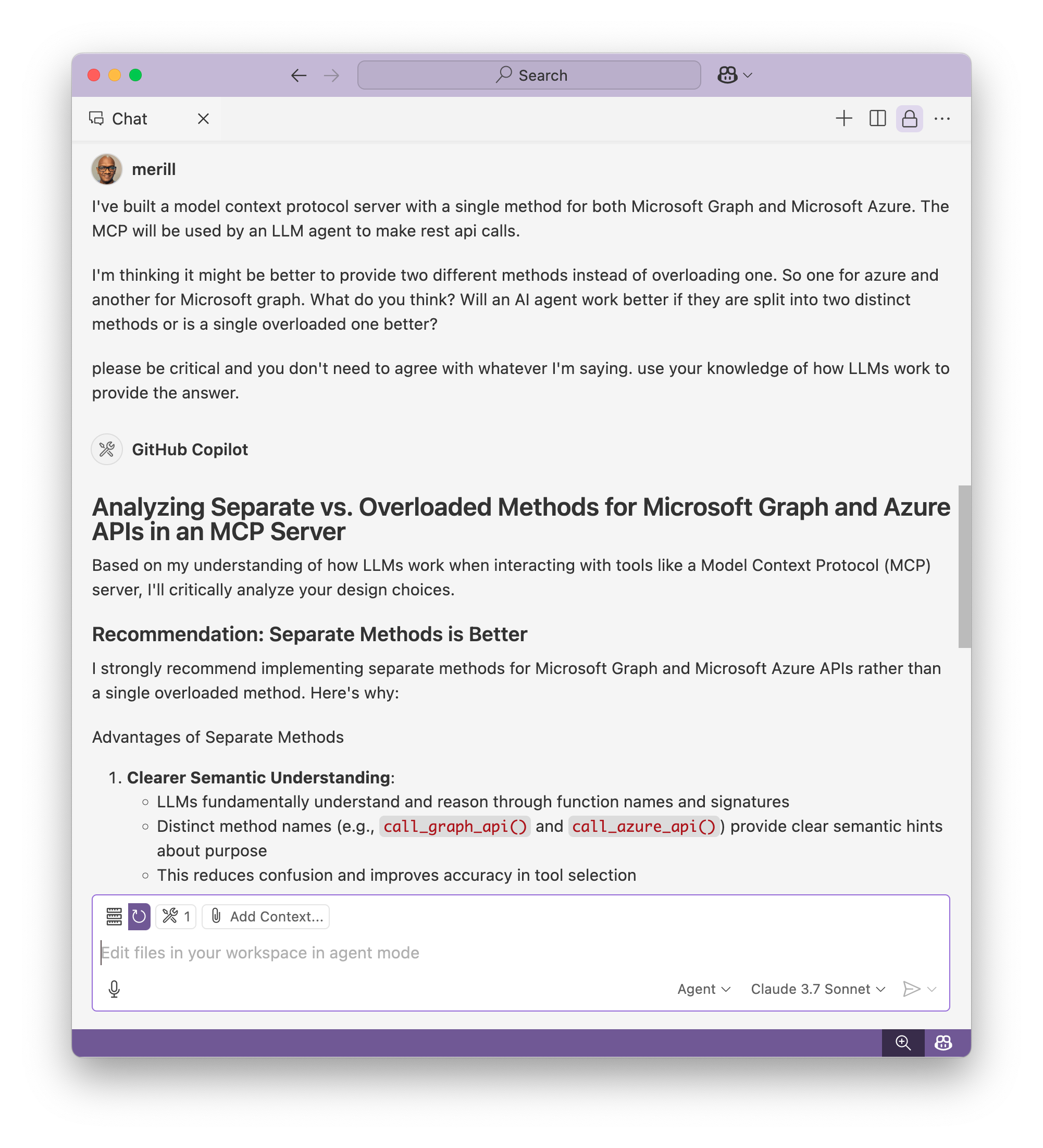
TwitterHow I use AI as a second brain
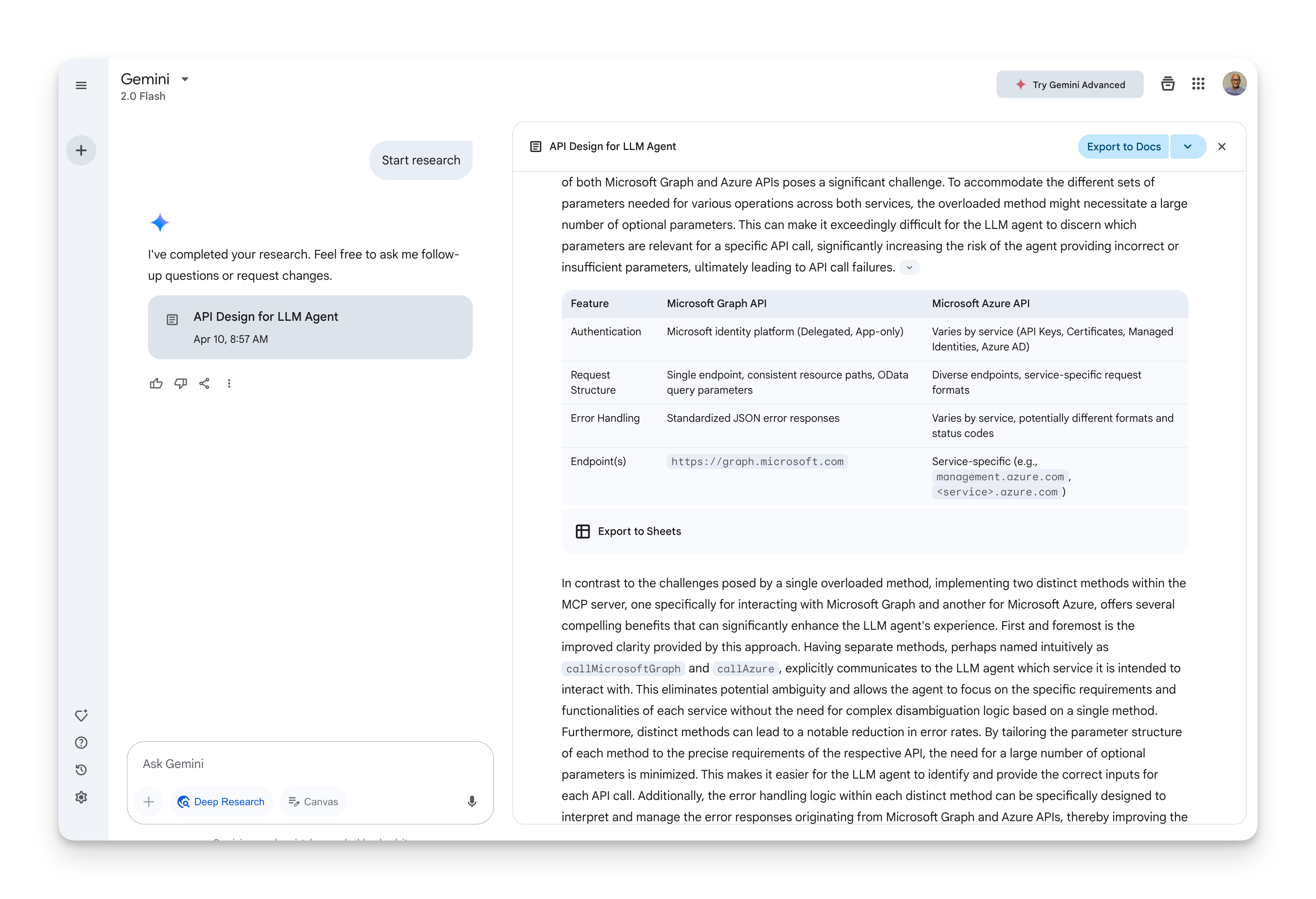
This is the start of a conversation I had with an AI to think through the design of changes I’m making to Lokka.
So far I’ve been mostly using GitHub Copilot and others to do specific tasks but I’m now starting to have design discussions and conversations to look for areas that I might be missing (or to play devils advocate).
I also pitted the LLMs against each other. Here’s a comparison.
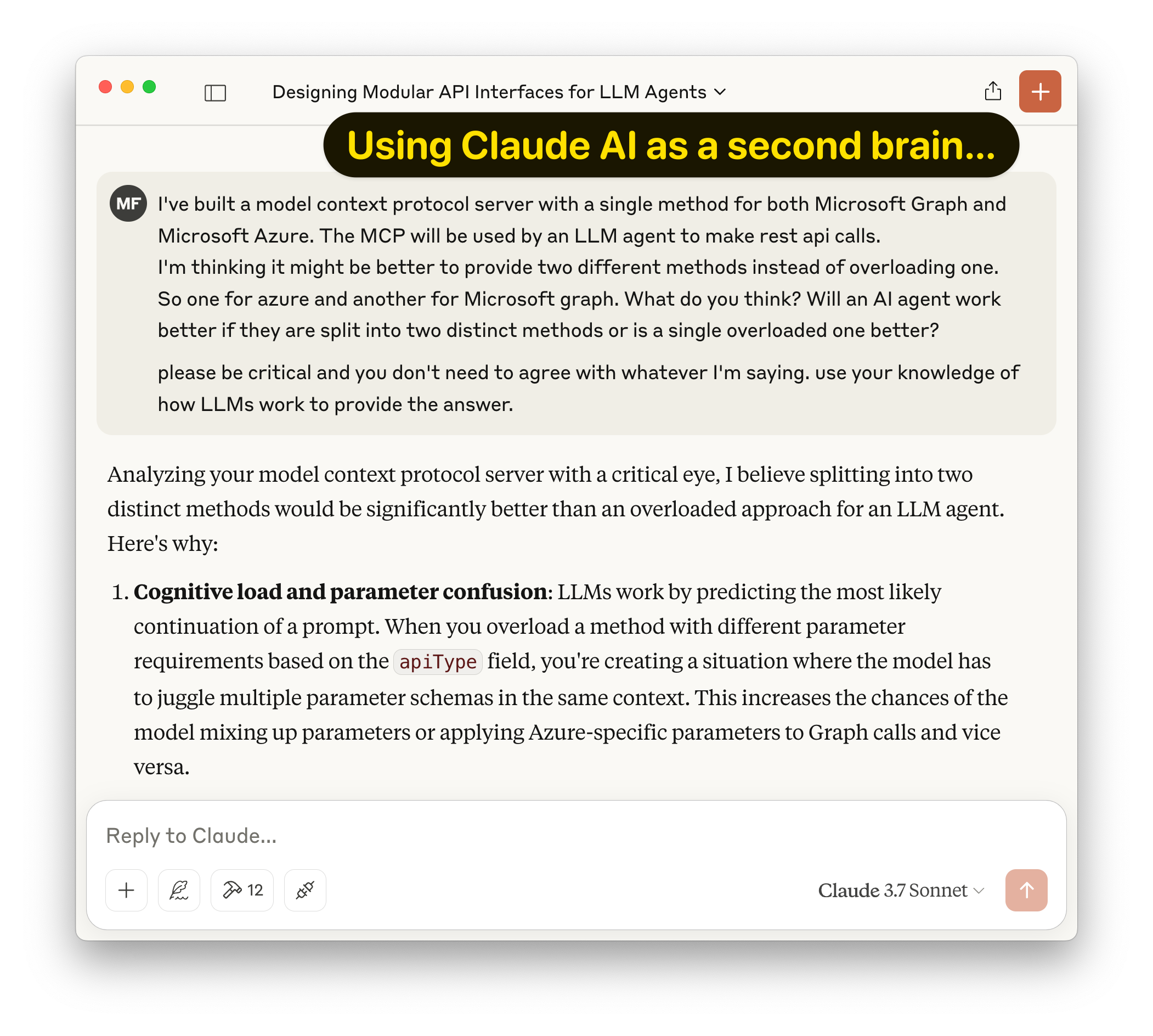
Claude provided a nice clean summary while GitHub Copilot is not just for code, it’s great for design thinking too.
The last one I tried was Google Gemini’s Deep Research which looked up over 190+ sites including Microsoft docs, LLM docs to provide a complete four page report. Very impressive.
Share on
TwitterMy projects

If you find them useful please leave a note!
Microsoft Community
Utilities that anyone in the Microsoft community will find useful.
- lokka.dev - An AI agent tool that brings the power of Microsoft Graph to AI agents
- cmd.ms - Your Microsoft Cloud command line.
- maester.dev - Microsoft test automation framework + security analyzer.
- akaSearch.net - Community contributed search engine for aka.ms links
- Microsoft 365 Message Center Archive - Searchable archive of all Microsoft 365 Message Center posts.
- Refined Microsoft Learn - Browser extension to make Microsoft Learn distraction free and focus on the content.
- bluesky.ms - Find Microsoft folks on Bluesky.
Microsoft Entra
Utilities for Microsoft 365 and Microsoft Entra admins and cybersecurity folks.
- Entra.News - Stay up to date on all things Entra with this weekly newsletter.
- Entra.Chat - A weekly podcast on Microsoft Entra.
- idPowerToys.merill.net - Microsoft Entra related power toys including a Conditional Access visualizer and Entra mind maps.
- aka.ms/AppNames - Repository hosting a daily updated csv/json of Microsoft first party app names and their GUIDs
- Entra Exporter - PowerShell module that exports all the config and data of a Microsoft Entra tenant.
- Azure AD Assessment - Guidance to assess the health of an Azure AD tenant.
- MSIdentityTools - Collection of useful cmdlets for common Azure AD functionality
Microsoft Graph
Utilities for everyone that works with Microsoft Graph and Graph PowerShell.
- Graph X-Ray - Fiddler for Microsoft! Convert your actions in the Azure Portal to Graph PowerShell commands.
- Graph Permissions Explorer - Site that shows all the Graph APIs and data exposed for a given Graph Permission.
Share on
TwitterLinkable identifiers in Microsoft Entra ID logs
Threat hunters rejoice! This is HUUUGE news.
Microsoft just introduced linkable identifiers in Microsoft Entra ID logs.
The bad guys are going to hate this so much.
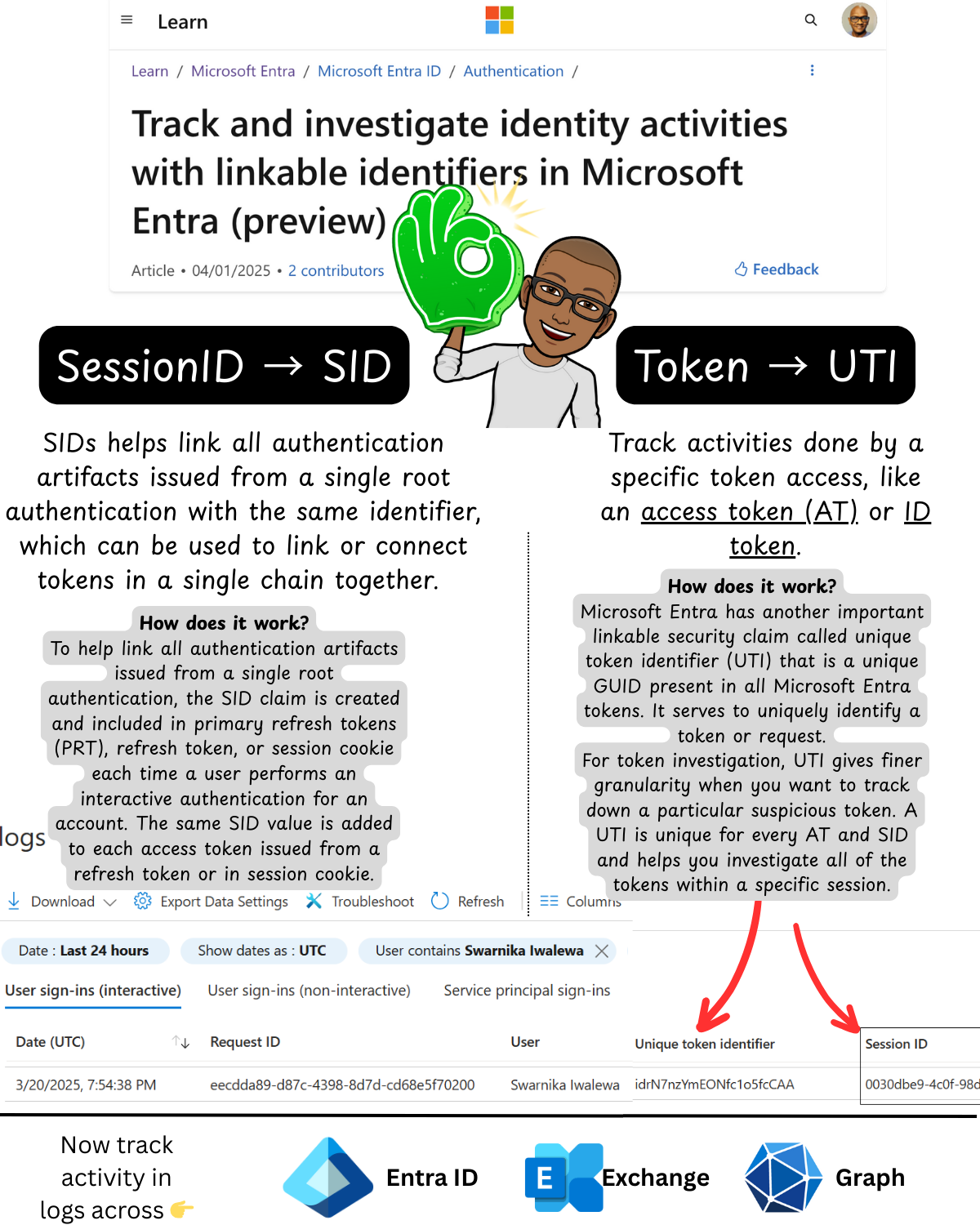
Learn more at Linkable identifiers in Microsoft Entra ID logs.
Share on
TwitterI just launched 🦋 Bluesky.ms!
🚀 I just launched my weekend hack project 🦋. With Twitter becoming unusable a whole heap of the Microsoft community is now on Bluesky and having a blast.
I made Bluesky.ms to make it easy to find each other. If you are already on Bluesky, add your profile so others can find you.
If you haven’t started on Bluesky here’s a primer.
🦋 What is Bluesky?
Bluesky is a social app that is designed to not be controlled by a single company. It’s an open network and a version of social media where it’s built by many people, and it still comes together as a cohesive, easy-to-use experience.
✅ Where do I sign up
- Web → Bluesky Web app
- iPhone → Bluesky iOS app
- Android → Bluesky Android app
🚀 How do I find people?
Rebuilding all the folks you know or finding people with similar interests take time. Here are some neat ways to bootstrap the process.
✅ Starter Packs
These are lists of Bluesky users that you can bulk follow. The starter packs help you quickly get started on Bluesky and follow folks in the Microsoft community.
See bluesky.ms/starterpacks for the latest list.
You can also find other non-Microsoft starter packs over at blueskydirectory.com/starter-packs
✅ Help others find you
If you write about Microsoft content and want others to find you, add your profile over at bluesky.ms.
This crowd sourced database welcomes everyone. If you find it’s missing anyone please feel free to add them in.
Let’s build some awesome open communities!